MACsec Feature
A Novel Approach to Encrypt Network Traffic
A Novel Approach to Encrypt Network Traffic
Taipei, Taiwan, Oct 04, 2022—There are a high number of sensitive files at places with a low tolerance for security hazards, such as banks, military bases, and governments. In addition to the onsite guard, efforts should be made to maintain network security since LANs are exposed to a variety of security dangers, and the economic damage caused by data leakage can be considerable. To protect hackers from intercepting sensitive data, functionality such as MACsec is designed. MACsec, or Media Access Control Security, protects data transmitted between Ethernet-connected devices. IEEE defined MACsec in 2006 (standard IEEE 802.1AE-2006). Originally designed to safeguard the link between two physically linked devices, Media Access Control Security may now secure data transfers between two devices regardless of the number of intervening devices or networks.
One of the most convincing reasons to use MACsec is that it provides Layer 2 security (OSI data link layer). The Data Link layer is used to send data across network entities while maintaining interoperability and interconnection with other levels. As a result, it is the most essential network layer to defend and is most vulnerable to assaults. "Network security is just as strong as the weakest link," as the saying goes, and Layer 2 is no exception. If the hacker gains access to Layer 2, communication may be jeopardized without the other levels being aware of the issue. A high degree of security is planned for the upper levels (OSI Layers 3 and above), but it is useless if Layer 2 is breached. Being a layer 2 protocol, MACsec may secure not just IP traffic, ARP, neighbor detection, and DHCP.
Packets in MACsec fo across "secure channels" that are backed by "secure associations." MACsec can detect and prevent the majority of security threats, such as denial of service, intrusion, man-in-the-middle, masquerade, passive eavesdropping, and playback assaults. Intrising understands just how important it is to protect Layer 2, which makes us start to equip our industrial equipment with MACsec. MACsec is our new feature that can be found on our product to protect your network security even better. Almost all traffic on an Ethernet link is secured by MACsec, including frames from the Link Layer Discovery Protocol (LLDP), Link Aggregation Control Protocol (LACP), Dynamic Host Configuration Protocol (DHCP), Address Resolution Protocol (ARP), and other protocols that are typically not secured on an Ethernet link due to limitations with other security solutions. Compared to TLS/SSL and IPsec, MACsec has lower latency since it can start at the header, has faster line rate speeds, and has superior performance utilizing hardware; in fact, numerous off-the-shelf chip vendors provide inbuilt MACsec functionality. As data is authenticated to the device, MACsec is aware of any changes to the data.
When MACsec is enabled, each packet sent over the wire is encrypted. Using MACsec in your network has various advantages:
- Discretion. MACsec safeguards data against illegal access. An unauthorized user should not be able to access data content. As a result, MACsec ensures secrecy through the use of powerful encryption.
- Virtue. Virtue means preventing unauthorized changes to data. A process in place is needed to identify data manipulation. As a result, MACsec performs an integrity check to avoid data tampering and ensure that data is not changed while in transit.
- Versatility. We can enable/disable MACsec on any chosen interface on a MACsec-enabled device.
- Intelligence on the Network. Because MACsec is a hop-by-hop encryption protocol, it does not conceal the content of data from network devices. Hop-by-hop encryption means that data is decrypted on the entrance port and encrypted on the egress port. On a network device, the data will be in plain text.
MACsec Key Agreement (MKA)
Intrising's MACsec feature can be enabled using static CAK mode and dynamic CAK mode. Static CAK security mode provides security by constantly refreshing to a new random security key and simply transferring the security key between the two devices on the MACsec-secured point-to-point link. When you enable MACsec in static connectivity association key (CAK) security mode, two security keys are used to secure the point-to-point Ethernet link: a connectivity association key (CAK) that connects control plane traffic and a randomly generated secure association key (SAK) that secures data plane traffic. To guarantee link security, both keys are frequently transferred between both devices on either end of the point-to-point Ethernet network.
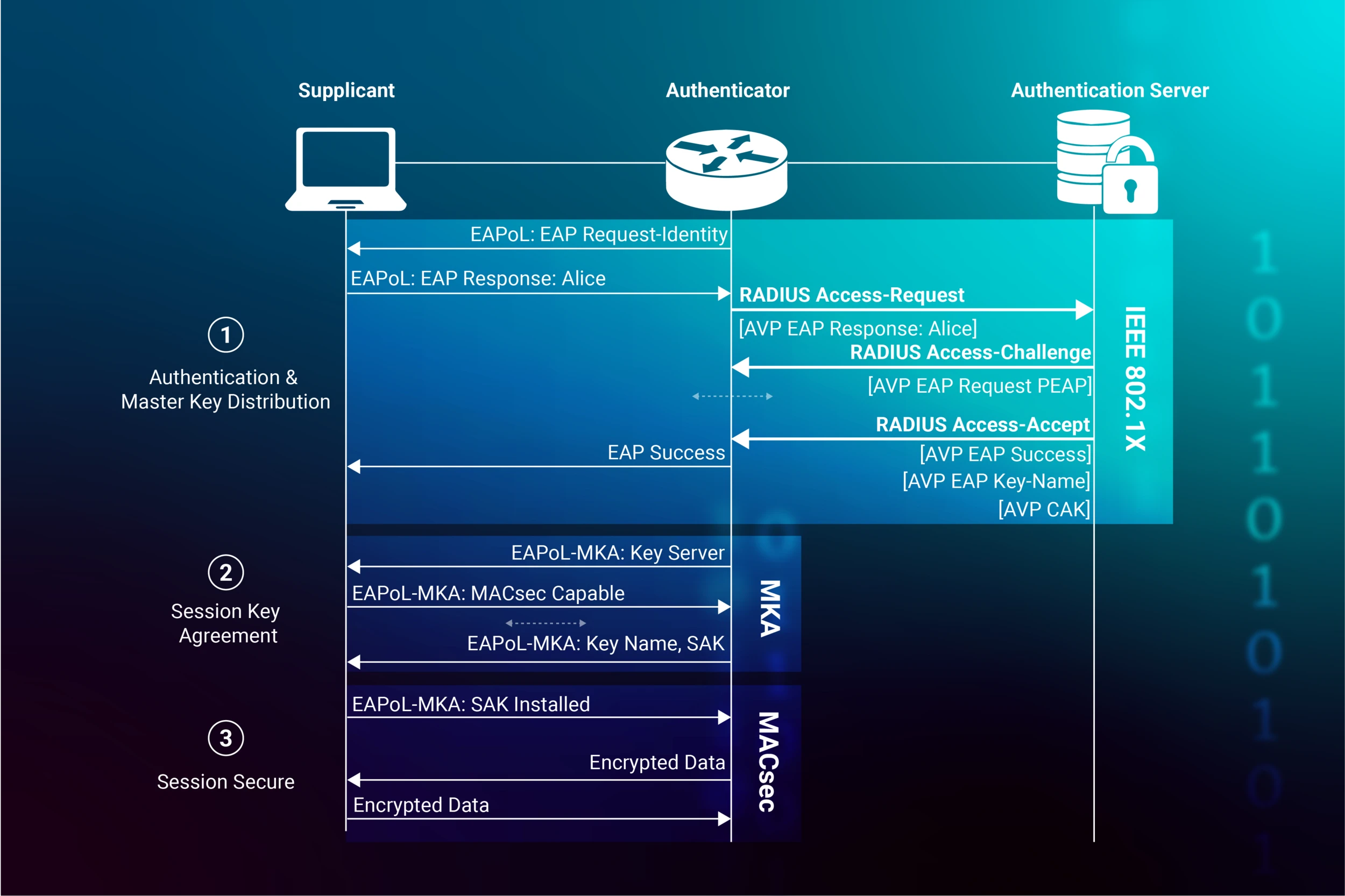
A static CAK security mode has its connectivity association key (CAK) and a connectivity association name (CKN). The user configures the CKN and CAK in the connectivity association, and they must match on both ends of the link to enable MACsec for the first time. After successfully exchanging matching pre-shared keys, the MACsec Key Agreement (MKA) protocol is activated. The MACsec Key Agreement protocol is in charge of preserving MACsec on the Ethernet network and determining which switch on the point-to-point link shall act as the key server. The key server will then generate a SAK that will only be shared with the switch on the other end of the point-to-point link, and that SAK will be used to protect any data traffic transiting the link.
The following are some optional MACsec capabilities that are only accessible when you enable MACsec utilizing static CAK security mode:
- Tagging with SCI. Allows the Secure Channel Identifier (SCI) tag to be included in the Security TAG (SecTAG) field of the MACsec header. The Secure Channel Identifier (SCI) tag in the Security TAG (SecTAG) field of the MACsec header is made up of a globally unique MAC Address and a system-specific port identifier.
- The ability to exclude MACsec traffic. The authenticated device is guaranteed to have delivered the received MAC frame.
In dynamic CAK mode, the security keys are generated dynamically by the peer nodes on the MACsec connection as part of the 802.1X authentication procedure. During authentication, peer nodes receive MACsec key characteristics from the RADIUS server and utilize these attributes to construct the CAK and CKN dynamically. The keys are then exchanged to establish a MACsec-secured connection. Because they keys do not need to be set manually, dynamic CAK mode makes administration easier than static CAK mode. Furthermore, the keys may be controlled centrally via the RADIUS server. Dynamic CAK mode can be used to secure a switch-to-host link or a link between switches or routers. The switch is the 802.1X authenticator on a switch-to-host link, while the host is the supplicant. The devices on a connection linking switches or routers must functions as both authenticators and supplicants to authenticate each other. Dynamic CAK mode is based on certificate-based validation through the use of an Extensible Authentication Protocol (EAP).
EAP authentication methods include message digest 5 (MD5), transport layer security (TLS), tunneled TLS (TTLS), protected extensible authentication protocol (PEAP), microsoft challenge-handshake authentication protocol version 2 (MSCHAPv2), password authentication protocol (PAP). The following are the characteristics of these method protocols.
- EAP-MD5: EAP-MD5 secures message exchange by producing a unique "fingerprint" to digitally sign each packet and assure the authenticity of EAP messages. EAP-MD5 is "lightweight" and conducts operations rapidly, making it simple to implement and configure.
- EAP-TLS: EAP-TLS is an extremely secure protocol that allows mutual authentication between the client and the authentication server. EAP-TLS is best suited for setups that already have PKI certificate infrastructure in place.
- EAP-TTLS: EAP-TTLS (Tunneled TLS) is an extension of EAP-TLS that gives the benefits of strong encryption without the complication of mutual certificates on both the client and authentication server. EAP-TTLS, like TLS, provides mutual authentication but only requires the authentication server to be authenticated to the client via a certificate exchange. EAP-TTLS simplifies deployment and maintenance while maintaining high security and authentication.
- PEAP: Protected EAP Protocol (PEAP) is an Internet-Draft that, in terms of mutual authentication capabilities, is comparable to EAP-TTLS and is presently being suggested as a replacement for EAP-TTLS by RSA Security, Cisco, and Microsoft. PEAP supports different EAP authentication methods and protects communication over a TLS-encrypted tunnel.
- EAP-MSCHAP-V2: A form of mutual authentication that allows for password-based user or computer authentication. Both the client and the authentication server must demonstrate knowledge of the user's password during the EAP-MS-CHAP v2 authentication procedure for authentication to succeed. Mutual authentication is accomplished by adding an authenticator packet delivered to the client following successful server authentication.
- PAP: PAP uses a two-way handshake to establish users' identities using basic password-based authentication. PAP sends passwords in plaintext over the network without encryption. If the Lightweight Directory Access Protocol (LDAP), which only accepts plaintext passwords for client authentication, is used for RADIUS authentication, PAP must be set.



